Mobile App Penetration Testing: Android & iOS
Mobile App Penetration Testing: Android & iOS Mobile App Penetration Testing: Android & iOS Comprehensive…
Mobile App Penetration Testing: Android & iOS Mobile App Penetration Testing: Android & iOS Comprehensive…
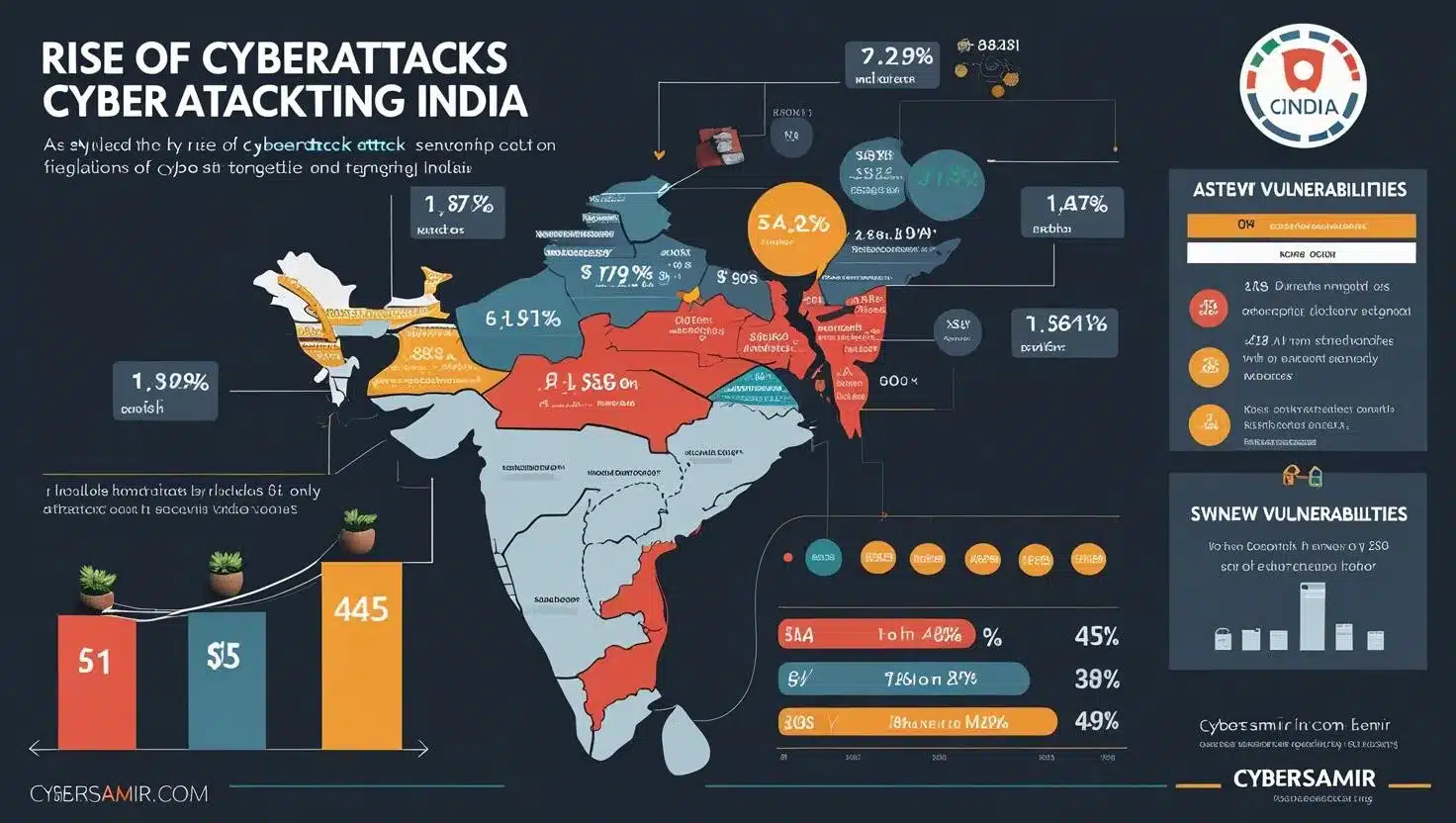
Why India Is Becoming a Prime Target for International Hackers Why India Is Becoming a…
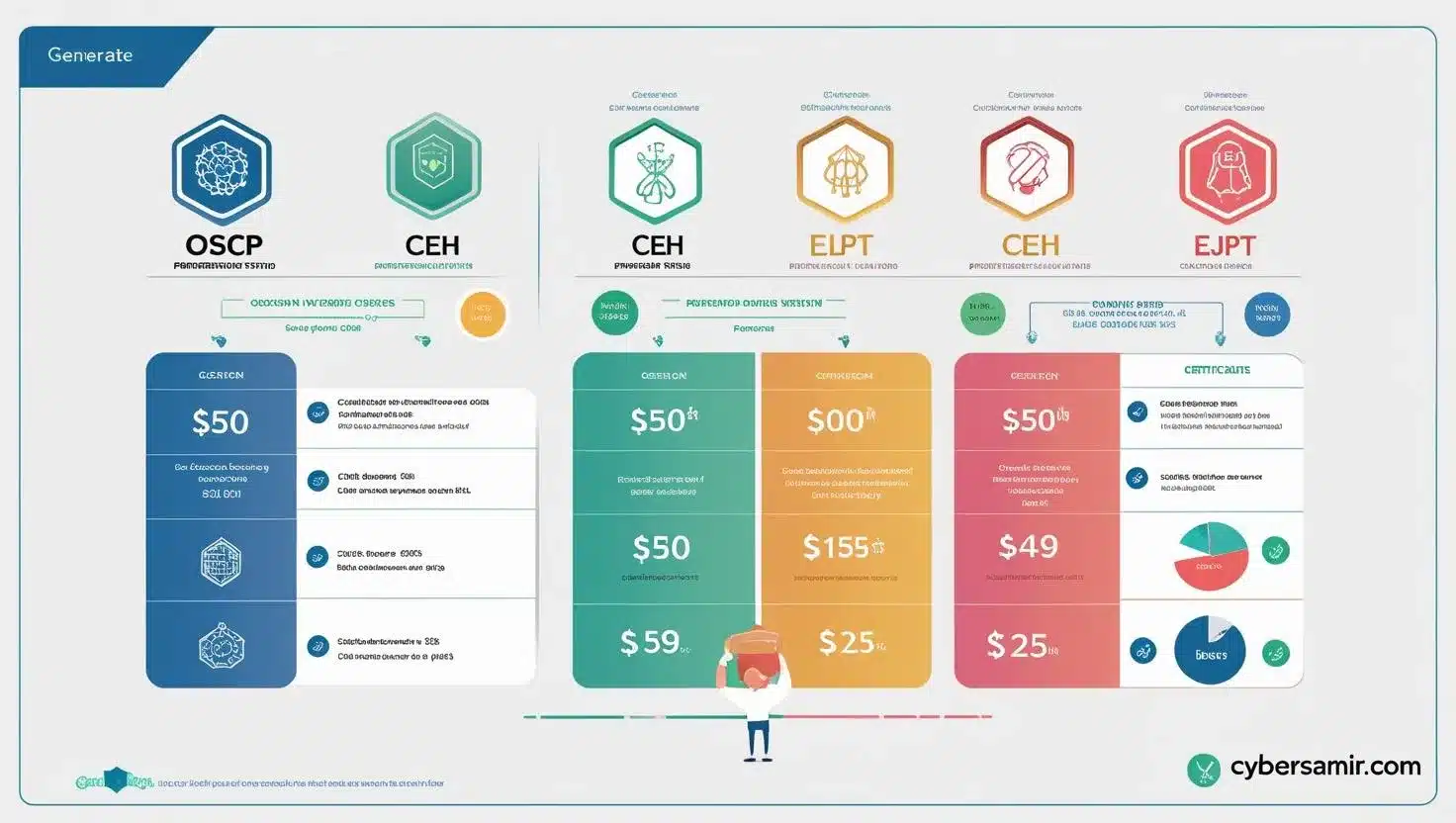
Penetration Testing Certifications: OSCP, CEH, eJPT Compared Penetration Testing Certifications: OSCP, CEH, eJPT Compared An…
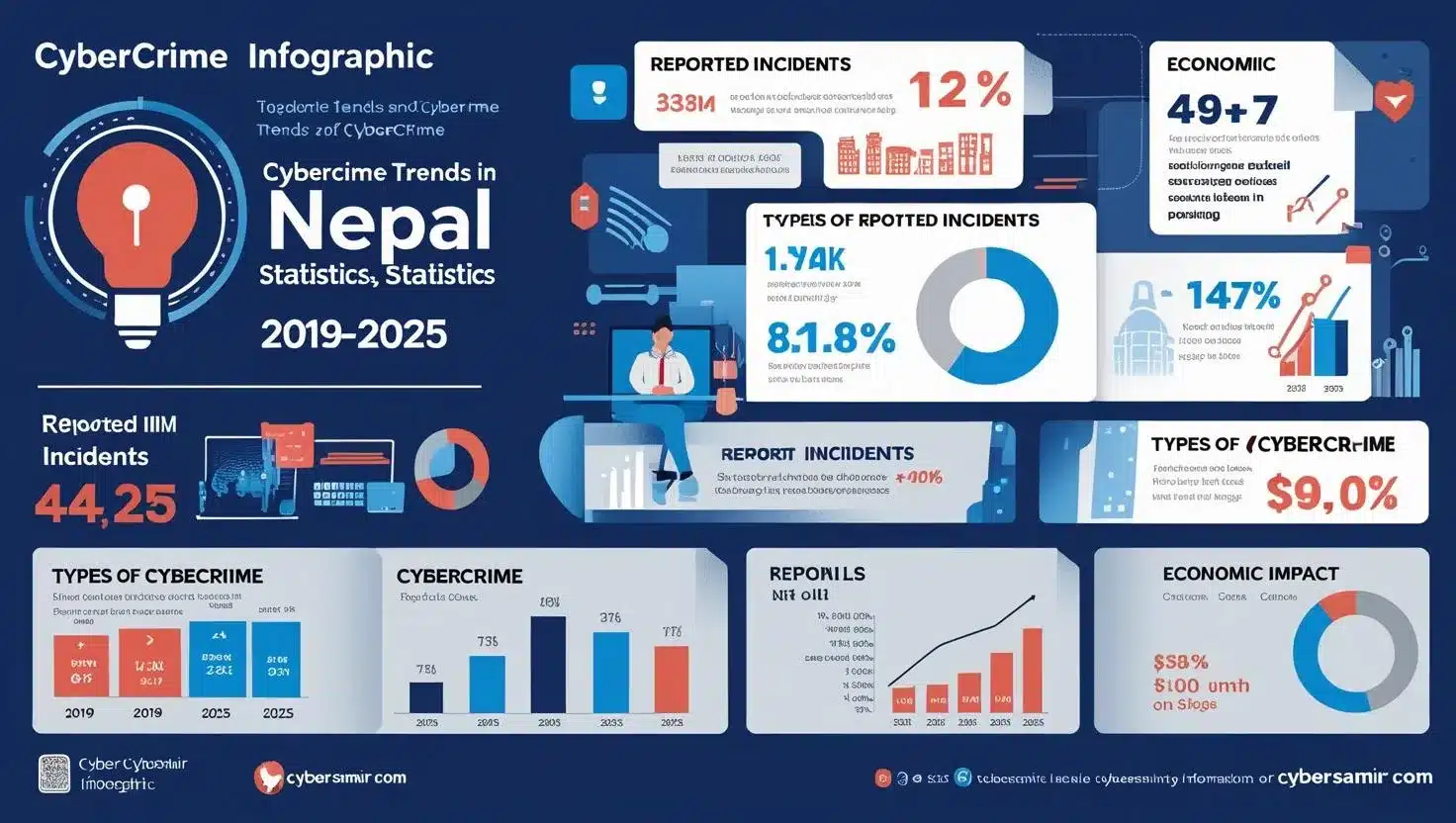
Cybercrime in Nepal: Trends & Statistics (2019-2025) | CyberSamir Cybercrime in Nepal: Trends & Statistics…

Bug Bounty Programs: How Hackers Get Paid to Find Vulnerabilities Bug Bounty Programs: How Hackers…

Cybersecurity in Nepal 2025: Complete Guide to Threats, Laws & Protection | CyberSamir Cybersecurity in…

How Deepfake Technology Can Be Used for Cybercrime How Deepfake Technology Can Be Used for…
What is an API? API Security Vulnerabilities What is an API? API Security Vulnerabilities An…

Nepal’s Banking Cybersecurity: Is Your Money Really Safe? Nepal’s Banking Cybersecurity: Is Your Money Really…
1. Keyboard Shortcuts Global Shortcuts Shortcut Action Ctrl+Shift+D Switch to Dashboard Ctrl+Shift+T Switch to Target…